‘We will set up an IT army’ twittered Vice President Federov of Ukraine. Delta asked cybercrime researcher Rolf van Wegberg how this will be done and who will be involved.
Even non-hackers can help by paying a small amount for a DDoS attack. (Photo: Max Bender/Unsplash)
Russian banks, companies and bitcoin suppliers are the first targets in the digital war that is lurking in the shadow of the military invasion. The objective of the ‘digital resistance’ is to cause disruption. This is surprisingly easy to do says cybercrime researcher Dr Rolf van Wegberg. He investigated whitewashing practices while studying criminology at the University of Leiden. At TU Delft, Van Wegberg earned his doctorate in 2020 with his dissertation entitled Outsourcing Cybercrime. He now works as Assistant Professor at the Faculty of Technology, Policy and Management at TU Delft.
The order for cyber attacks was issued by the IT Army of Ukraine (@ITarmyUA). It shares its targets through an account on the Telegram chat service and currently has close to 40,000 followers. The intention is to disable the websites listed, explains Van Wegberg.
The easiest way to do this is through a DDoS (Distributed Denial of Service) attack that sends so much traffic to the target that its website becomes inaccessible. This tactic was used by what turned out to be an 18 year old pupil in the Dutch province of Brabant to disable the Tax Authority’s website. The attack was surprisingly effective.
‘Who carries out an attack is not relevant to a country in war’
Van Wegberg explains that even non-hackers can help by paying a small amount for a DDoS attack. You do not even need to be on the Dark Web to do this. Shady service providers present themselves in a good light as testers of the strength of a network or the speed of a connection. These are other terms for the same mechanism as DDoS.
Carrying out a DDoS attack is a criminal offence, and the effect is only temporary. As soon as the targeted traffic is stopped, the site is accessible again.
Advanced attacks are done using malicious software (‘malware’) that can cause permanent damange or that can take over the control of systems or industrial complexes.
One spectacular example is the Anonymous activist group that has taken over Russian television channels and broadcast images from Ukraine into Russian living rooms, regardless of which channel people were watching.
Another far reaching claim is from Network Battalion 65 (@NM65ukraine) that boasts that ‘DDoS is not our style. We prefer to hack and slash’. They claim to have sabotaged control over Russian photo satellites. This is supposed to have disabled the air traffic control system last Monday. This brings cyber warfare and battlegrounds together.
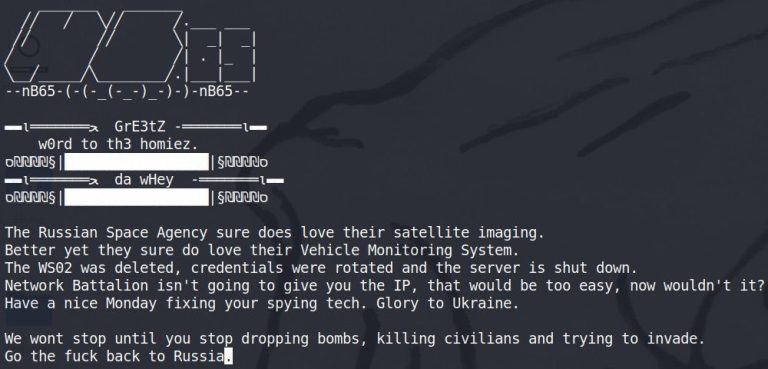
Hackers group Network Battalion 65 annoinces the take-over of a Russian satellite system.
The question is if the means justify the end. Van Wergberg is pragmatic. “Who carries out an attack is not relevant to a country in war. The enemy of my enemy is my friend.”
Daily Dot editor Mikael Thalen noted on Twitter a historic change in cyber morals. ‘Has anyone else taken a moment to stop and think about the fact that we’re basically witnessing an unprecedented moment out of cyberpunk lore where nation states are green-lighting hacktivism campaigns as part of a major military conflict … or just me?’
Do you have a question or comment about this article?
j.w.wassink@tudelft.nl


Comments are closed.